Cookies help us to deliver certain functionalities to you and to guarantee the best user experience possible. By continuing to browse and use this website you agree to our use of cookies in accordance with our Privacy Policy.
Cookies help us to deliver certain functionalities to you and to guarantee the best user experience possible. By continuing to browse and use this website you agree to our use of cookies in accordance with our Privacy Policy.
The Niagara Networks 3808E is a flagship, carrier-grade hybrid platform that combines dual-protection bypass technology with advanced packet broker capabilities to deliver one of the industry’s highest-density solutions for inline high-availability and visibility. Designed for high-performance networks, the 3808E supports up to eight network links - configurable as bypass segments or active TAPs - providing unmatched flexibility for a wide range of inline security use cases. Its powerful feature set includes sophisticated load balancing, traffic flow/packet filtering, and TAP aggregation, all integrated into a single modular solution that simplifies deployment and reduces total cost of ownership. Compared to traditional solutions, it delivers up to 400% higher bypass segment density per single RU for 40/100Gb environments, making it ideal for complex, multi-vendor security stacks. With support for all major interface speeds (1/10/25/40/100Gb), a pay-as-you-grow modular design, and API-driven automation for fail-safe scenarios, the 3808E redefines inline security with performance, scalability, and operational efficiency.
3808E
The Niagara Networks 3299 is a compact, multifunctional solution that combines hybrid bypass TAP functionality with a fully featured network packet broker. It delivers 1Gb bypass and active TAP versatility, supporting a broad range of deployment scenarios, from inline security tool resilience to traffic monitoring and network visibility.
3299
The Niagara Networks 3296 Bypass Switch is a multi-rate, modular passive bypass switch that supports up to 8 network links to ensure failsafe connectivity for inline security appliances. The system is designed with four modular bypass segments (up to 8 total segments) and features a customized USB Type interface for specialized management and API development purposes.Note: This model is intended for special use cases only. For more information, please contact our support team.
3296
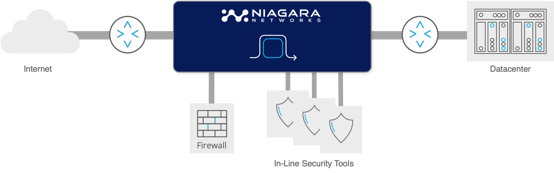
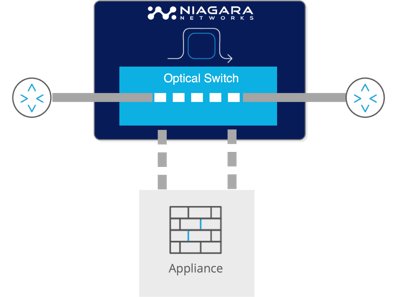
Normal operation of a network bypass:
The traffic between 2 network elements (ie: router, switch) go through an inline network security tool
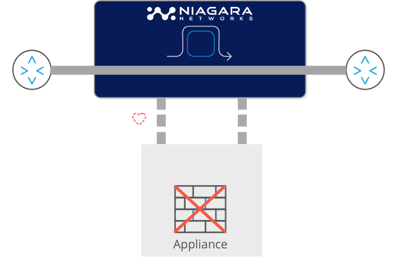
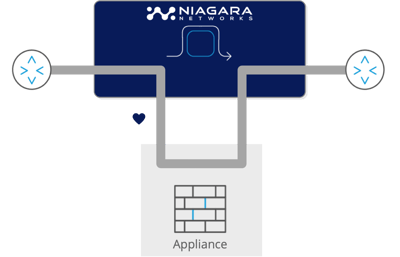
In the case of a failure of the inline tool/appliance -
the bypass makes sure the traffic between the network elements remains up and running
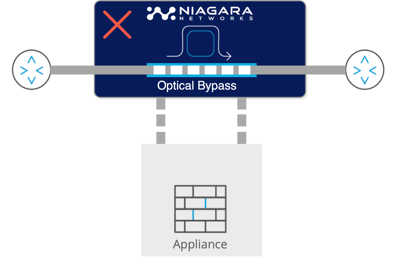
In the case of power failure of the bypass switch itself,
the traffic between the network elements continues to flow thanks to optical/copper relay
Protecting network traffic flow in case of Bypass failure
When power fails, the optical-relays in the bypass switch ensure that the network flow continues uninterrupted. The optical relays can be configured fail open or fail close to meet specific deployment needs.
This ensures uninterrupted network services under all conditions.
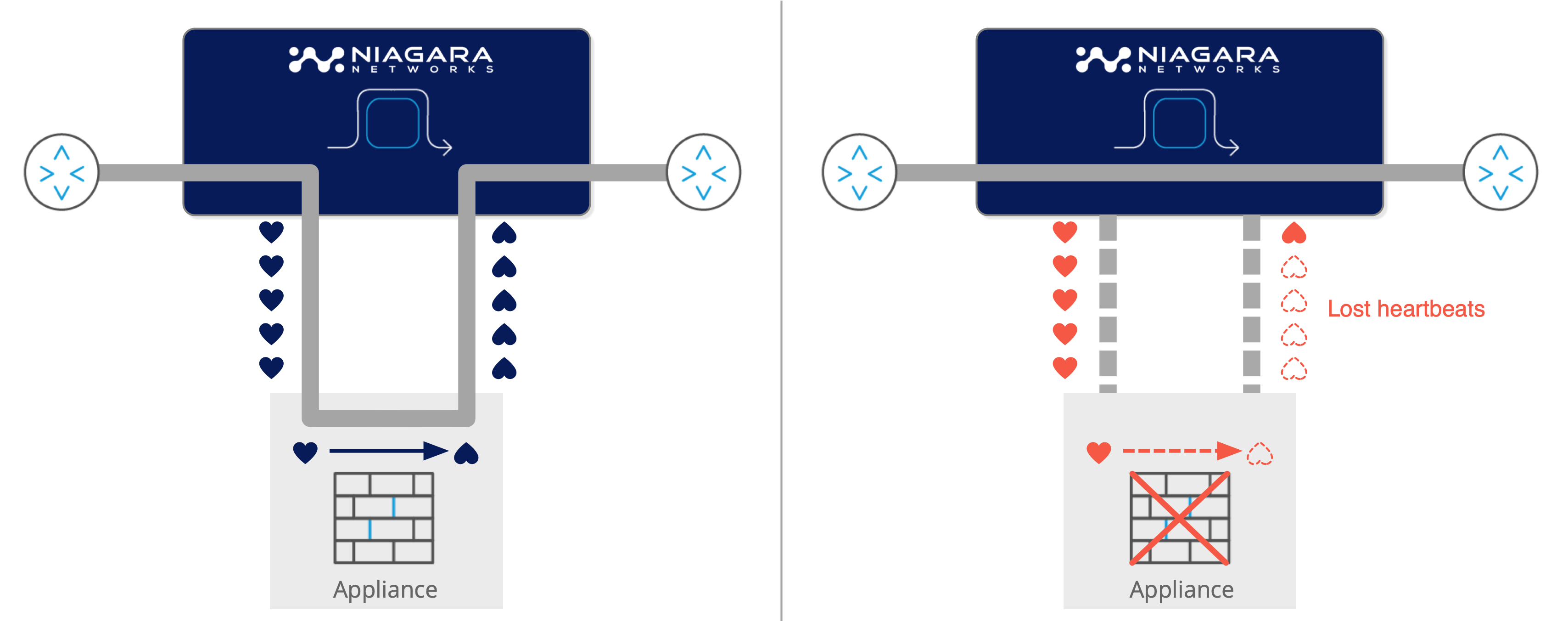
Protecting network traffic flow in case of appliance failures
The Bypass transmits a user-configurable heartbeat on the appliance ports. In the event of an appliance malfunction (such as a software crash, system failure or loss of power), the failure is detected, and the Bypass redirects the traffic intended for the inline appliance to the network ports, allowing it to continue to flow through the network link. This feature also enables the network appliances or network security tools to be removed and replaced without network downtime. Once the system is backed up, or the power is restored to the appliance, it is detected by the Bypass heartbeat mechanism, and network traffic is seamlessly diverted back to the inline device, allowing it to resume its critical functions.
© 2025 Niagara Networks. All Rights Reserved.